[ad_1]
Greater than a month earlier than Russia invaded its former Soviet neighbour, dozens of Ukrainian authorities web sites had been taken down earlier than returning with a warning: ‘put together for the worst.’
Consultants say Russian hackers — state and proxy — have been pummelling their neighbour for years, releasing devastating data-wiping malware and even briefly taking down the nation’s energy grid in a sample of assaults which have induced mayhem far past the Ukraine.
So, as troops loomed on the border, governments around the globe feared a serious cyber assault might be launched at any second.
However, three weeks into the battle, such motion stays to be seen. Relatively than battering transport providers or taking healthcare techniques offline, solely restricted, unsophisticated assaults appear to have been levelled towards Ukraine.
‘Cyber operations take a very long time’
In fact, no-one is aware of what’s being deliberate within the battle rooms of the Kremlin. And regardless of years of worldwide funding and a casual military of anti-Putin hackers, Ukraine’s energy grid, for instance, is arguably nonetheless susceptible to Russian cyber ops.
However in occasions of battle, these sorts of large-scale infrastructural assaults may very well be a poor use of assets, specialists instructed Metro.co.uk.

‘Cyber operations take a very long time,’ stated cybersecurity researcher Sneha Dawda from the Royal United Companies Institute. ‘It’s not easy to create a bit of malware that might disrupt the entire power infrastructure of Ukraine.’
The form of refined assault wanted to take out a transport community or an influence grid requires intimate information of a goal system — its entry factors, its entry credentials — stated Esther Naylor, a analysis analyst at Chatham Home’s Worldwide Safety Programme.
That is information Russia merely might not have, regardless of its reported use of its neighbour as a ‘take a look at mattress’ for cyber ops. These might have given Ukraine the chance to study how its neighbour hacks, giving it time to adapt its cybersecurity efforts in response, Dawda added.
On some measures, Ukraine is much less ‘cyber mature’ than Russia. Again in 2020, it ranked 78th in comparison with Russia’s 5th on the Worldwide Telecommunications Union’s World Cyber Index, for instance.
However stacking up one nation’s cyber capabilities towards one other isn’t any actual science, Dawda defined, and the nation could have made enhancements during the last two years.

The very fact Russia’s cyber assaults have been ‘nowhere close to the size that was anticipated’ may counsel Ukraine has made itself a tougher goal. Nevertheless it additionally may point out Russia sees ‘a bodily offensive as simpler.’
‘Cheaper to drop bombs’
It’s doable the nation already has a cyber weapon in its arsenal it simply hasn’t deployed. However it will be costly and time-consuming to develop new infrastructure-busting malware.
And proper now, Russia is funding a serious invasion while dealing with crippling financial sanctions. Dear cyber assaults with lengthy lead occasions will not be a sustainable approach of utilizing restricted assets.
Critical cyber operations are ‘so arduous and costly,’ Dawda stated, that it could merely be ‘cheaper to drop bombs.’
‘While you’re bombing hospitals, whenever you’re bombing civilian infrastructure… It doesn’t make sense to attempt to take down the facility grid as a result of you are able to do that with shelling,’ added Naylor.

That’s to not say that cyber operations don’t play a major function in battle. However they could not all the time come as blockbuster assaults.
As a substitute, it could be simpler to make use of cyber as an adjunct to conventional warfare: a option to improve disruption and promote an environment of chaos.
So, how do governments do that? And the way may these sorts of operations have an effect on you?
Creating chaos on the battlefield
On the battlefield, governments might use cyber operations to immediately disrupt their opponent’s army tools and comms.
Though these capabilities are high secret, the UK did reveal particulars of 1 profitable cyber marketing campaign.
Between 2016 and 2017, British intelligence operators used cyber strategies to jam telephones, disrupt drones and intrude with servers utilized by terrorist group ISIS.

Jamming telephones, for instance, is believed to have hampered communication between ISIS commanders and people combating on the bottom, leaving them misdirected and even lower off.
‘We wished to deceive them and to misdirect them, to make them much less efficient, much less cohesive and sap their morale,’ Strategic Command commander Basic Sir Patrick Sanders instructed Sky Information final yr.
It was essential, he added, to verify these actions befell alongside bodily operations.
‘You possibly can’t simply try this in our on-line world. You must coordinate and combine [it] with actions which are happening on the bottom, whether or not it’s from our personal forces, particular forces and others.’
Hitting ISIS servers with malware served one other essential goal: disrupting the movement of propaganda used to radicalise and recruit new members. Along with the US, British operators locked ISIS members out of their accounts, eliminated on-line posts and deleted materials saved on their servers.
Within the wake of this operation, the UK arrange the Nationwide Cyber Pressure – a collaboration between the army, GCHQ, MI6 and defence lab Porton Down.
Exterior of the battlefield, governments are extremely involved a couple of cyber risk that hits far nearer to house: the rampant unfold of disinformation.
Affect operations
A trademark of quite a few governments’ cyber exercise — throughout peacetime and in battle — is the creation, dissemination and amplification of faux information. Whether or not shared by state media shops or unfold by pro-government teams, false info is commonly used to sway public opinion and affect political debate.
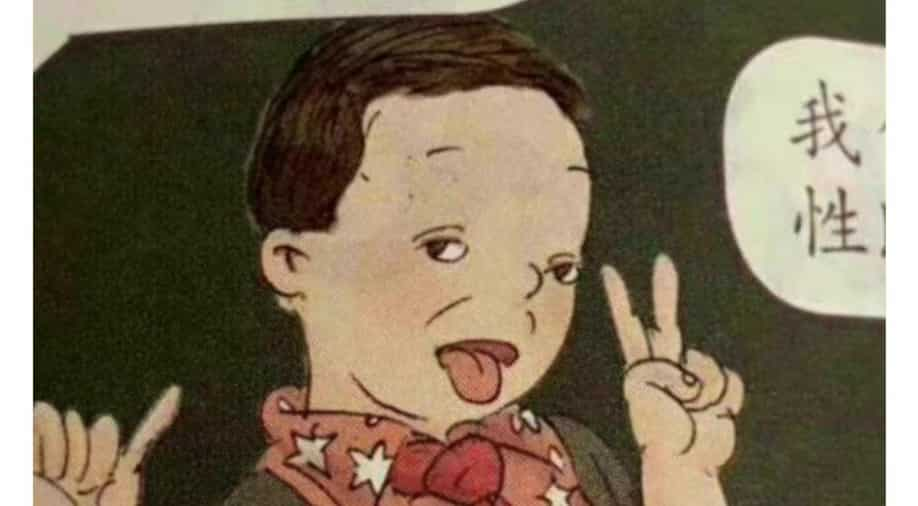
Final summer time, researchers with the Centre for Data Resilience recognized a community of social media accounts utilizing pretend information and different techniques to push pro-China narratives and encourage discord within the West.
CIR director of investigations Benjamin Strick stated the group gave the impression to be attempting to ‘delegitimise the West by amplifying pro-Chinese language narratives.’
He added: ‘The community targets important topics comparable to U.S. gun legal guidelines, Covid-19, human rights abuses in Xinjiang, abroad conflicts and racial discrimination in an obvious bid to inflame tensions, deny remarks vital of China, and goal Western governments.’
Pushing false narratives on social media is just not the only protect of authoritarian regimes. Former U.S. president Donald Trump was well-known for making false and deceptive statements on his Twitter account. A lot in order that he was completely banned from the platform final January within the wake of the Capitol riot.

Russia is very skilled at utilizing pretend information to wield affect on-line. Throughout the pandemic, pro-Kremlin networks and state media shops used pretend information to criticise mRNA jabs and accuse the EU of political bias in its evaluation of the nation’s Sputnik V vaccine.
The nation has employed this acquainted playbook towards Ukraine for years. Now, alongside its bodily invasion, it’s placing increasingly more of its efforts into sharing lies concerning the nation.
This ‘downpour’ of disinformation is probably going getting used to ‘conceal the bottom realities’ and ’trigger chaos,’ in accordance with Chatham Home researcher Isabella Wilkinson.
‘Very usually, one might say this goals to trigger a smoke and mirrors impact: to behave as a smokescreen,’ she defined. ‘This enables a tighter management of the data setting. And as we all know, info is so highly effective.’
A lot of the fabric being shared — posts calling a pregnant blogger a ‘disaster actor’, or claiming actors on a film set are parading as injured civilians — implies Ukraine is falsely presenting itself as a sufferer of battle.
Different disinformation, like baseless claims on state TV that Ukraine is planning to nuke Russia, are getting used to justify Putin’s false pretext for invasion: that Ukraine — and typically its allies — had been an imminent hazard.
Concerningly, officers from China have been spreading some of these fake stories even additional.
Fertile floor for ‘poisonous’ disinformation
Social media, whether or not it’s Fb, Twitter and now TikTok, may be fertile floor for a ‘poisonous mixture’ of disinformation and misinformation, the place deliberate makes an attempt to deceive are unwittingly amplified by customers unaware they’re spreading pretend information, Wilkinson stated.
In Russia, which has applied strict guidelines on journalism and restricted entry to world information shops and social media, the variety of dependable sources accessible to residents to problem state narratives is shrinking.

When you’re unlikely to be immediately impacted by battlefield cyber ops, there’s a great likelihood you’ll come throughout pretend information in some kind should you’re on social media. And these aren’t remoted to intervals of battle.
‘It’s actually essential to recognise that the current actions and data operations focused towards Ukraine aren’t essentially distinctive,’ Wilkinson stated.
‘They’re actually simply a part of Russia’s long term playbook of data operations there.’
Though these operations might usually begin on-line, they’re normally designed to have an effect on the true world. Governments and proxies can use pretend information to attempt to flip the tide of public opinion of their favour, for instance by spreading lies about political opponents or inflaming tensions overseas.
If sufficient individuals imagine the lies — or not less than cease trusting their very own authorities — disinformation actors could possibly affect elections, undermine help for international governments and, within the case of Russia and Ukraine, construct help for a battle.
Defending your self from cyber operations
Cyber ops — whether or not they take the type of disinformation, denial of service assaults, malware or surveillance — aren’t restricted to governments or to battle time. So, it’s essential to be vigilant everytime you use the web.
To guard your self from disinformation:
- Be cautious of tales that appear stunning or surprising. Ask your self if there is perhaps an ulterior motive behind them.
- Attempt to confirm the creator of a social media put up or a information article. The place has it been revealed? Are they a dependable supply?
- Test if a number of dependable shops reporting the identical story
- If you happen to aren’t acquainted with a selected outlet, see if it’s recognized for sharing disinformation by Googling it or checking if it’s on an inventory of recognized pretend information web sites, like this one from PolitiFact.
- Until you’re assured a narrative is true, don’t share it.
To guard your self from malware:
- Use totally different passwords for various accounts, and don’t share them with anybody. You should utilize a password supervisor to maintain observe of them in the event that they’re arduous to recollect.
- Change the default password issued together with your router. If it’s not clear how to do that, contact your web service supplier.
- Use two-factor authentication the place its accessible
- Be cautious of clicking on hyperlinks in emails, particularly if the sender is unfamiliar or the URL appears to be like suspicious.
- Hold your apps updated.
- If you happen to’re involved about privateness, verify what permissions an app will use prior to installing it.
The UK’s Nationwide Cyber Safety additionally has an inventory of straightforward guidelines to guard your self towards malicious assaults.
However the accountability isn’t simply on us. Authorities companies just like the Nationwide Cyber Pressure have been set as much as shield the UK from dangerous cyber assaults. The company, which is ready to develop this yr, can also be considered engaged in anti-disinformation actions.
‘We’re lucky within the UK, that we do have a authorities with totally different departments whose job it’s to give attention to these items,’ stated Naylor. ‘We’ve got emergency response groups even in every totally different authorities division.’
The UK’s newest cyber technique recommends shifting accountability on safety from person to supplier, with the federal government promising to take away ‘as a lot of the burden’ from people as doable.

Firms offering important providers are already required to abide by sure cybersecurity guidelines. The brand new technique guarantees laws and incentives might be up to date to encourage personal corporations to have interaction and put money into cyber resilience.
Large tech corporations have taken steps to fight disinformation on their platforms, however they’re repeatedly accused of being sluggish to take away dangerous content material.
Some specialists say the visible nature of disinformation shared on-line has made it notably arduous to determine and take away.
Policing visible content material may be difficult — particularly for newer platforms like TikTok, in accordance with Stanford Web Observatory technical analysis supervisor Reneé DiResta. She instructed CNN: ‘Fb and Twitter have had some fairly in depth expertise in content material moderation throughout crises; I believe TikTok is discovering itself having to rise up to hurry in a short time.’
Social media corporations have had some successes to date in eradicating pretend accounts. Fb introduced final month it had taken down a community of faux information shops and personas pushing anti-Ukrainian messages on its platform.
However with new false posts showing on-line on a regular basis, disinformation will certainly proceed to form — and deform — the battle in Ukraine.
MORE : Nameless claims it has taken out Russia’s nationwide safety company
MORE : Nvidia hit by cyberattack in order that they hack the hackers as revenge
[ad_2]
Source link