[ad_1]
Kick-start your journey to be a grasp reverser with the instruments and analytical prowess of Ghidra SRE. This is a information on the way to set up and arrange Ghidra in your Linux machine.
What Is Ghidra?
Created by the NSA, Ghidra is an open-source, cross-platform, refined software program reverse engineering framework that provides military-grade instruments for analyzing and reversing software program binaries. With Ghidra, you possibly can reverse engineer or, decompile a software program binary and research the supply code beneath.
It’s typically the go-to framework within the commerce of malware evaluation and reverse engineering, carefully competing with IDA, a software program reverse engineering framework of comparable stature.
Step 1: Putting in JDK 11
Earlier than exploring the Ghidra set up course of, it’s important to ensure that your system has JDK 11 put in and arrange. With out Java put in in your system, Ghidra will refuse to even begin up.
You’ll be able to both manually set up JDK 11 by downloading the tarball or set up it by means of the bundle supervisor of your Linux distro. Ideally, putting in through bundle managers is the best way to go because it’s a lot faster and hassle-free than the previous hands-on methodology.
To put in JDK 11 in your Linux desktop, fireplace up the terminal and run the next instructions relying in your distro’s bundle supervisor:
On Debian/Ubuntu-based programs:
sudo apt-get set up openjdk-11-jdkOn Arch-based programs:
sudo pacman -S jdk11-openjdkOn Fedora/CentOS/RHEL programs:
sudo dnf set up java-latest-openjdkStep 2: Putting in Ghidra
Ghidra SRE is not usually put in right into a system, and there is not a standard installer included with the Ghidra launch file. You simply should obtain the binaries, make them executable utilizing the chmod command, and run them from the terminal on the go.
Downloading Ghidra
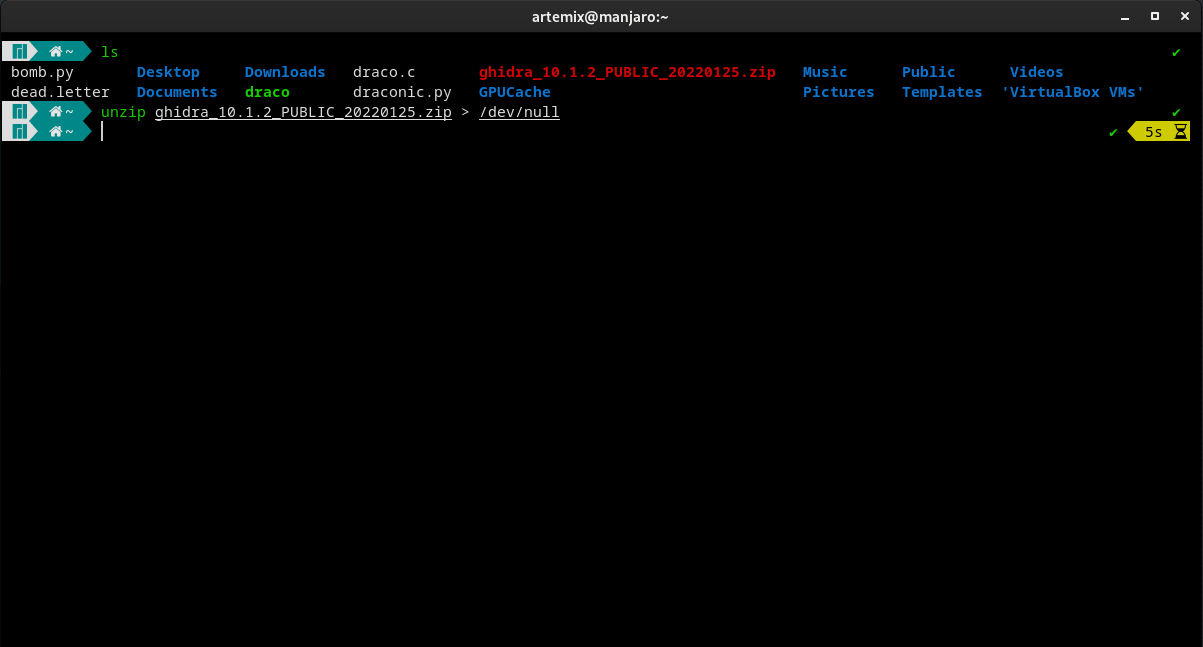
To start with, obtain the most recent Ghidra launch ZIP file from the official repository and extract it right into a listing. After you have extracted the information, transfer into the listing utilizing the cd command.
Word that downloading an older launch may be dangerous enterprise as Ghidra, being a Java software, was prey to the log4shell vulnerability. This safety flaw was fastened within the 10.1.1 replace. In order a security measure, attempt to keep away from utilizing variations previous to the most recent launch.
Obtain: Ghidra (Free)
Operating Ghidra
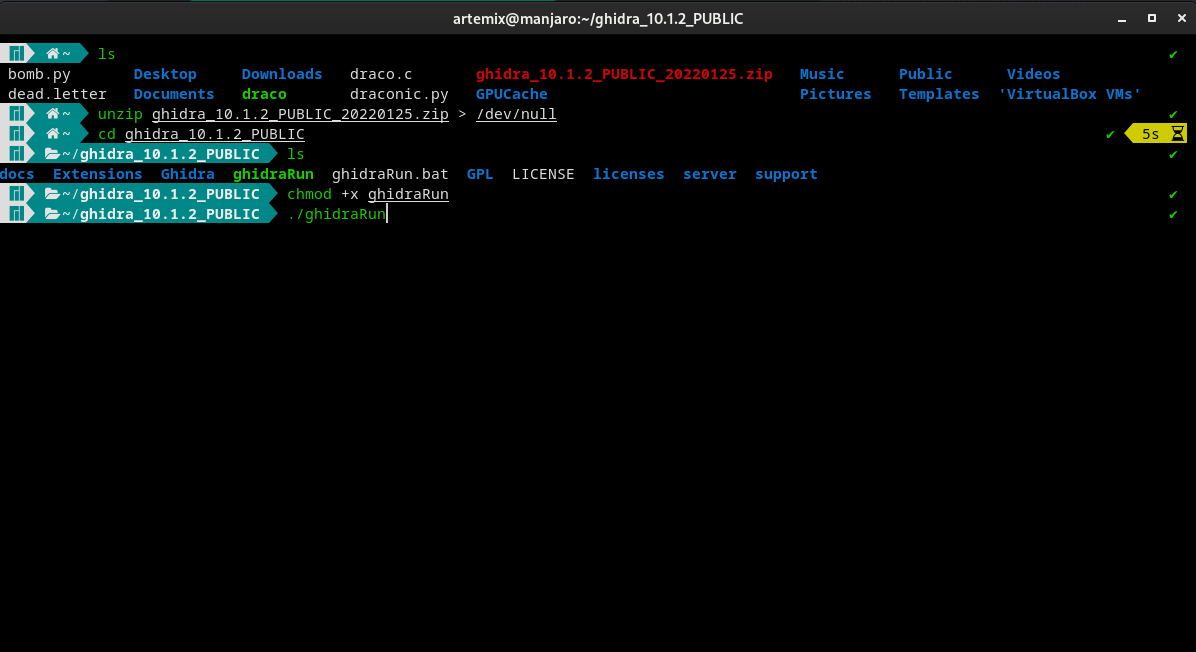
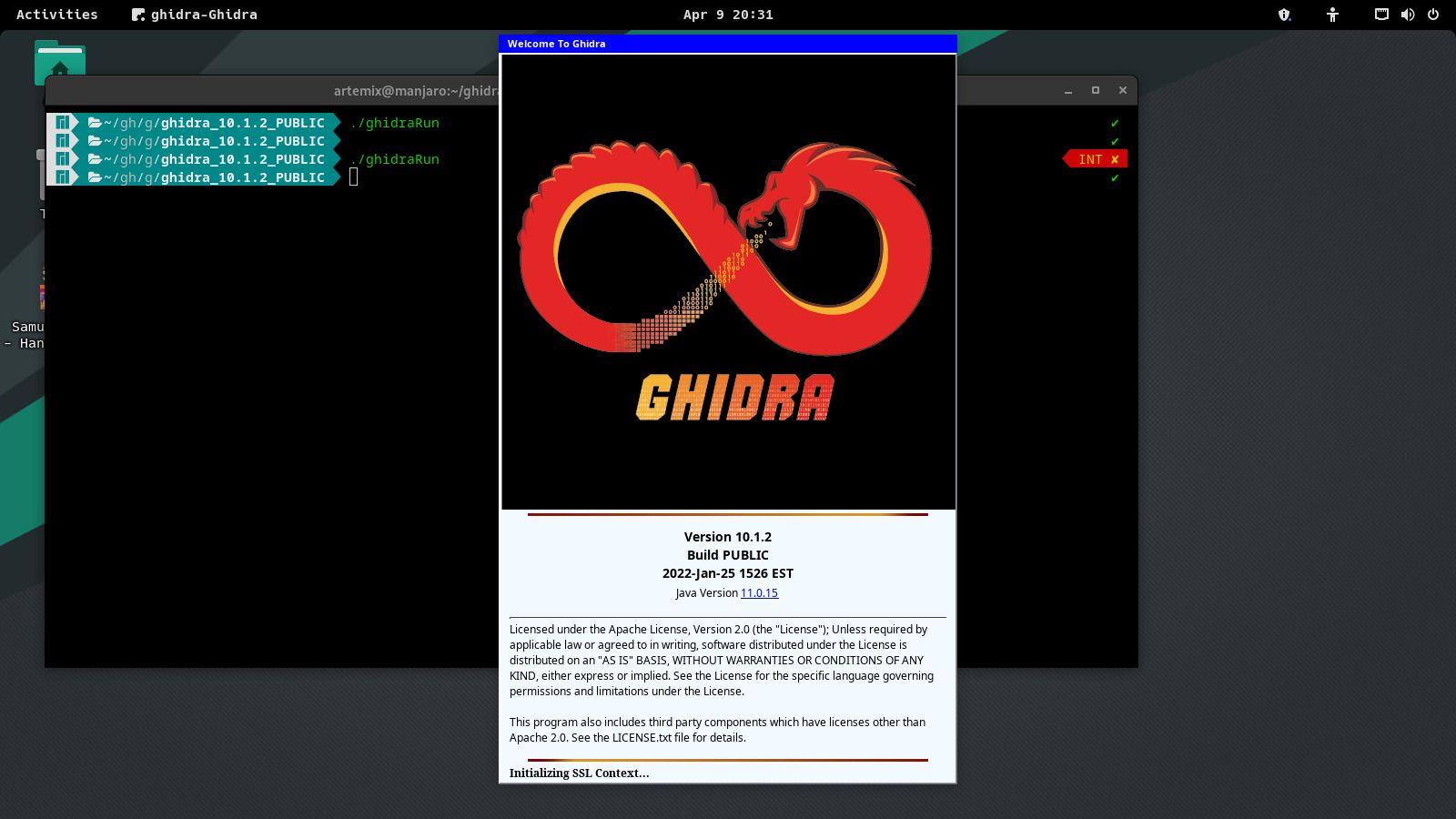
Among the many extracted information, one can find a file named ghidraRun. It’s a Bash script to launch Ghidra. Pop up a shell within the listing, make the file executable utilizing the chmod command, and run it from the command line utilizing the next instructions:
chmod +x ghidraRun
./ghidraRunThat ought to fireplace up Ghidra SRE. Click on on I agree, and you will be greeted with the Ghidra splash display.
Step 3: Making a Desktop Shortcut to Ghidra
As beforehand talked about, Ghidra is not shipped with an installer. So you will not discover Ghidra within the purposes menu or by looking within the app drawer in your Linux desktop.
If you end up regularly utilizing Ghidra, it may be a trouble to manually find the listing and fireplace it up from the terminal every time.
A easy answer to streamline this course of is to create a desktop shortcut to Ghidra. This is the way to create a desktop shortcut to Ghidra SRE:
- Create a desktop entry file and fill it with the info under:
[Desktop Entry]
Model=10.0
Kind=Utility
Terminal=false
Icon=/house/artemix/ghidra/help
Exec=sh /house/artemix/ghidra/ghidraRun.sh
Identify=Ghidra - Exchange the info within the Icon and Exec fields with the situation of the Ghidra icon and the launch script in your machine.
- Save the file as “Ghidra.desktop” within the Desktop listing.
- Proper-click on the file and set it to Enable Launching or fireplace up a terminal and use the chmod command to make it executable for all customers.
chmod a+x Ghidra.desktop
Now, you possibly can launch Ghidra straight from the desktop shortcut you simply created. Saves you a variety of effort and time every time that you must work with Ghidra.
Reverse engineering is the method of decompiling a software program binary to review and modify its supply code. It’s a refined method utilized by safety professionals to investigate and neutralize malware.
Though Ghidra’s modularity, portability, and in depth characteristic set have made it a fan favourite amongst professionals and amateurs alike, there are many security-based alternate options so that you can select from.
Learn Subsequent
About The Creator
[ad_2]
Source link